In this issue — 4 parts
Part 1 of 4
Identity Theft Has Become a Factory Assembly Line
The Problem: Identity Theft Has Become a Factory Assembly Line
Imagine a criminal organization that does not rob banks directly. Instead, they steal house keys from millions of people, sort them by neighborhood, package the best ones, and sell them to burglars who specialize in specific areas. Each person in the chain has one job; no single individual needs to understand the full operation. The key copier never meets the burglar. The packager never visits the house. It is an assembly line for theft.
Now add artificial intelligence to every step of that assembly line. The key-copying is automated and runs around the clock. The sorting is instant, powered by machine learning that identifies which keys belong to the most valuable properties. The fake identification documents are flawless deepfakes generated in seconds. The burglars are AI programs that never sleep, never take a day off, and can attempt thousands of break-ins simultaneously.
That is what identity theft looks like in 2026. It is no longer a single criminal sitting in a dark room trying passwords one at a time. It is a fully industrialized supply chain with specialized roles, professional services, quality control, and customer support for buyers of stolen identities.
PwC's "Cyber Threats in Motion" report, published in early 2026, documents this transformation in stark detail. The report reveals that identity compromise has evolved from an opportunistic crime into a structured, scalable business operation. Every stage of the attack lifecycle now has dedicated operators, tools, and marketplaces. Criminal groups have adopted the same principles that made legitimate businesses efficient: specialization, automation, and supply chain optimization.
The implications for organizations are severe. Traditional security measures were designed to defend against individual attackers probing for weaknesses. They were not built to withstand an industrial operation that can harvest millions of credentials in a single campaign, verify them within hours, and deploy them against targeted organizations within days.
What makes this particularly dangerous is the velocity of the operation. A credential stolen on Monday can be verified by Tuesday, listed for sale by Wednesday, purchased by a threat actor on Thursday, and used to breach a corporate network by Friday. The entire chain from theft to compromise can complete in less than a business week. Many organizations do not even realize their credentials have been stolen until weeks or months after the initial harvest.

Identity theft in 2026 operates like an industrial supply chain, with specialized roles at every stage from credential harvesting to monetization.
Why This Matters to You
If your organization uses passwords, single sign-on, or cloud services (and nearly every organization does), your credentials are a commodity on criminal marketplaces right now. The question is not whether your identities will be targeted; it is whether they have already been stolen and are sitting in a broker's inventory waiting for a buyer.
PwC found that the average time between credential theft and its use in an attack has shortened dramatically, yet many organizations still rely on periodic password resets and basic multi-factor authentication as their primary defense. These measures are no longer sufficient against an industrialized adversary.
Coming up in Part 2 — the six specialized phases that turn a stolen credential into monetized access.
Part 2 of 4
The Six-Phase Identity Attack Supply Chain
What you missed: identity theft is no longer a lone criminal act — it runs like a factory assembly line with specialized stages.
What Happened: The Six-Phase Identity Attack Supply Chain
PwC's research maps the identity attack ecosystem into six distinct phases. Each phase has its own specialists, tools, and economics. Understanding this chain is critical because defending against it requires disrupting multiple links, not just one. Here is how it works, explained in plain terms.

The identity attack supply chain operates like a legitimate business, with specialized roles at every stage from harvesting to monetization.
Harvest
Think of it like this: Automated programs called "infostealers" sweep through millions of computers like a vacuum cleaner for credentials. They grab saved passwords from browsers, authentication tokens from applications, session cookies, and even autofill data. A single infostealer campaign can harvest credentials from hundreds of thousands of machines in a matter of hours. The operators do not care about individual victims; they care about volume.
These programs spread through phishing emails, malicious advertisements, pirated software downloads, and compromised websites. Once installed, they silently extract every stored credential on the machine and transmit them back to a central server. The victim rarely notices anything unusual.
Result: Millions of raw username and password combinations collected automatically, packaged into bulk data sets.
Broker
Think of it like this: Initial access brokers (IABs) are the middlemen of the criminal identity economy. They operate like wholesale distributors, purchasing raw credential dumps from harvesters and performing quality control. They verify which passwords still work, identify which organizations those credentials belong to, and categorize them by industry, company size, and value.
Brokers add value by curating their inventory. A raw dump of a million credentials might contain 80% outdated passwords. The broker tests each one, removes the dead entries, and packages the verified, working credentials into categorized listings. They often guarantee freshness, offering refunds or replacements if a credential stops working before the buyer can use it.
Result: Verified, categorized credential packages ready for sale, complete with metadata about the target organization.
Sale
Think of it like this: Criminal groups purchase verified identities through dark web marketplaces that function like underground e-commerce platforms. These marketplaces have search filters, customer reviews, pricing tiers, and escrow services. Buyers can search for credentials by target company, industry vertical, user role, or geographic region.
Pricing varies based on the perceived value. A basic employee credential for a small company might sell for $10 to $50. An administrator credential for a Fortune 500 company's cloud environment can fetch thousands of dollars. State-aligned threat groups often pay premium prices for credentials targeting critical infrastructure, defense contractors, or government agencies.
Result: Targeted purchases of specific credentials matched to the buyer's objectives and target profile.
Compromise
Think of it like this: The buyer uses stolen identities to log into company systems, most often through single sign-on (SSO) portals. Because the credentials are real (they belong to actual employees), the login appears completely legitimate. There is no brute force attack, no vulnerability exploitation, and no malware. The attacker simply walks through the front door with a stolen key.
If multi-factor authentication is in place, attackers use AI-generated deepfake voice calls or real-time phishing proxies to intercept the second factor. PwC documented cases where AI-powered voice clones called IT help desks to request MFA resets, impersonating the legitimate employee convincingly enough to bypass security protocols.
Result: Authenticated access to corporate systems that looks indistinguishable from normal employee behavior.
Lateral Movement
Think of it like this: Once inside, AI-powered tools map out internal systems with remarkable speed. The attacker's AI scans for connected services, shared drives, databases, and privileged accounts. It identifies which systems trust each other, finds escalation paths to higher-privilege accounts, and locates the most valuable data stores. What used to take a skilled attacker weeks of careful manual exploration now happens in minutes.
The AI also learns the organization's normal patterns of behavior so it can mimic them. It logs in during business hours, accesses files at the same frequency as the legitimate user, and avoids triggering volume-based alerts. It is patient, methodical, and nearly invisible to conventional monitoring tools.
Result: Complete map of internal systems, escalated privileges, and access to the organization's most sensitive data.
Monetization
Think of it like this: The final phase is cashing in. Attackers have multiple playbooks: exfiltrate sensitive data and sell it, deploy ransomware and demand payment, use the compromised environment to launch attacks on partner organizations, or sell the established access to the next buyer. Some groups run all four simultaneously to maximize returns on their investment.
In many cases, the access itself becomes a product. After extracting value, the attacker sells their foothold to another group that uses it for a different purpose. A ransomware group might sell their persistent access to a state-sponsored espionage team after the ransom has been paid, extending the compromise indefinitely.
Result: Data stolen, ransomware deployed, partner organizations targeted, or persistent access resold to the next buyer.
The "Shelf Life" Problem
Stolen credentials can sit unused in broker inventories for weeks or months before being purchased and deployed. This means your organization might already be compromised from a credential theft that occurred before your current security measures were in place. The password you changed six months ago may not matter if the attacker harvested a session token or authentication cookie that is still valid.
PwC found that the average dwell time (the gap between initial credential theft and its use in an attack) ranges from two weeks to six months. During this window, organizations have no indication that their credentials are circulating on criminal marketplaces. By the time the credential is used, the original theft has long been forgotten or overlooked. This delay is intentional; it makes it harder for defenders to connect the breach to its source.
Single Sign-On: Convenience vs Risk
"One login, access everything."
- ✓ Single password to remember
- ✓ Seamless access to email
- ✓ Seamless access to file storage
- ✓ Seamless access to CRM
- ✓ Seamless access to financial systems
- ✓ Seamless access to HR records
- ✓ Seamless access to code repositories
Designed for productivity: one trusted identity unlocks every connected service.
"One stolen login, access everything."
- ✗ Attacker reads all email and contacts
- ✗ Attacker downloads sensitive files
- ✗ Attacker exports customer data from CRM
- ✗ Attacker accesses financial records
- ✗ Attacker harvests employee PII from HR
- ✗ Attacker plants backdoors in code
- ✗ Attacker pivots to partner organizations
The same convenience that helps employees helps attackers: one stolen identity unlocks the entire environment.
SSO was designed with productivity in mind, not adversarial resistance. The same architecture that eliminates friction for employees also eliminates friction for attackers who hold valid credentials.
Coming up in Part 3 — how the financial damage cascades from a single stolen identity.
Part 3 of 4
The Cascading Cost of Stolen Identity
What you missed: the six phases (harvest, broker, sale, compromise, lateral movement, monetization), plus the credential 'shelf life' problem and the SSO convenience-versus-risk tradeoff.
The Cascading Financial Impact
The financial damage from identity compromise is not limited to the initial breach. Because modern organizations are deeply interconnected through cloud services, SaaS platforms, and API integrations, a single compromised identity can cascade across the entire digital ecosystem. PwC describes this as the "blast radius" problem: one stolen credential can detonate across every connected service, partner organization, and downstream system.
Consider a mid-level employee whose SSO credentials are stolen. That single login may provide access to email (containing sensitive client communications), cloud storage (containing contracts and financial projections), a CRM platform (containing customer records), an HR system (containing employee Social Security numbers), and a project management tool (containing strategic plans). Each of these systems connects to others through integrations and shared permissions. The attacker does not need to compromise each system separately; the SSO credential is the master key.
The direct costs include incident response, legal fees, regulatory fines, customer notification, credit monitoring services, and potential litigation. But the indirect costs are often larger: business disruption during remediation, loss of customer trust, damaged brand reputation, increased insurance premiums, and the opportunity cost of diverting leadership attention from strategic initiatives to crisis management.
Financial Impact
Credential monetization at scale, cascading access across interconnected cloud and SaaS environments, and geopolitically motivated targeting of critical infrastructure.
PwC's report also highlights the geopolitical dimension of this threat. State-aligned threat groups are increasingly purchasing credentials from the same criminal marketplaces used by financially motivated actors. The difference is their targets: critical infrastructure, defense supply chains, telecommunications providers, and government agencies. These groups are not looking for ransom payments; they seek persistent access for espionage, pre-positioning for future conflict, or the ability to disrupt essential services on command.
The convergence of criminal and state-sponsored activity on the same supply chain means that a credential stolen by a financially motivated infostealer operator can end up in the hands of a nation-state intelligence service. The employee whose browser password was harvested by a commodity malware campaign may have unknowingly provided the initial foothold for a strategic espionage operation.
Coming up in Part 4 — six steps to disrupt the identity supply chain.
Part 4 of 4
Six Steps to Disrupt the Supply Chain
What you missed: how the financial damage cascades, and why stolen identity is the entry point.
What You Can Do: Six Steps to Disrupt the Supply Chain
Defending against an industrialized identity supply chain requires thinking beyond traditional perimeter security. You cannot simply build higher walls when the attacker is walking through the front door with a valid key. Instead, you need to make stolen credentials less valuable, detect their misuse faster, and limit the damage when a compromise occurs. Here are six practical steps that any organization can begin implementing.
Effective defense requires a layered approach that disrupts the identity attack supply chain at multiple points simultaneously.
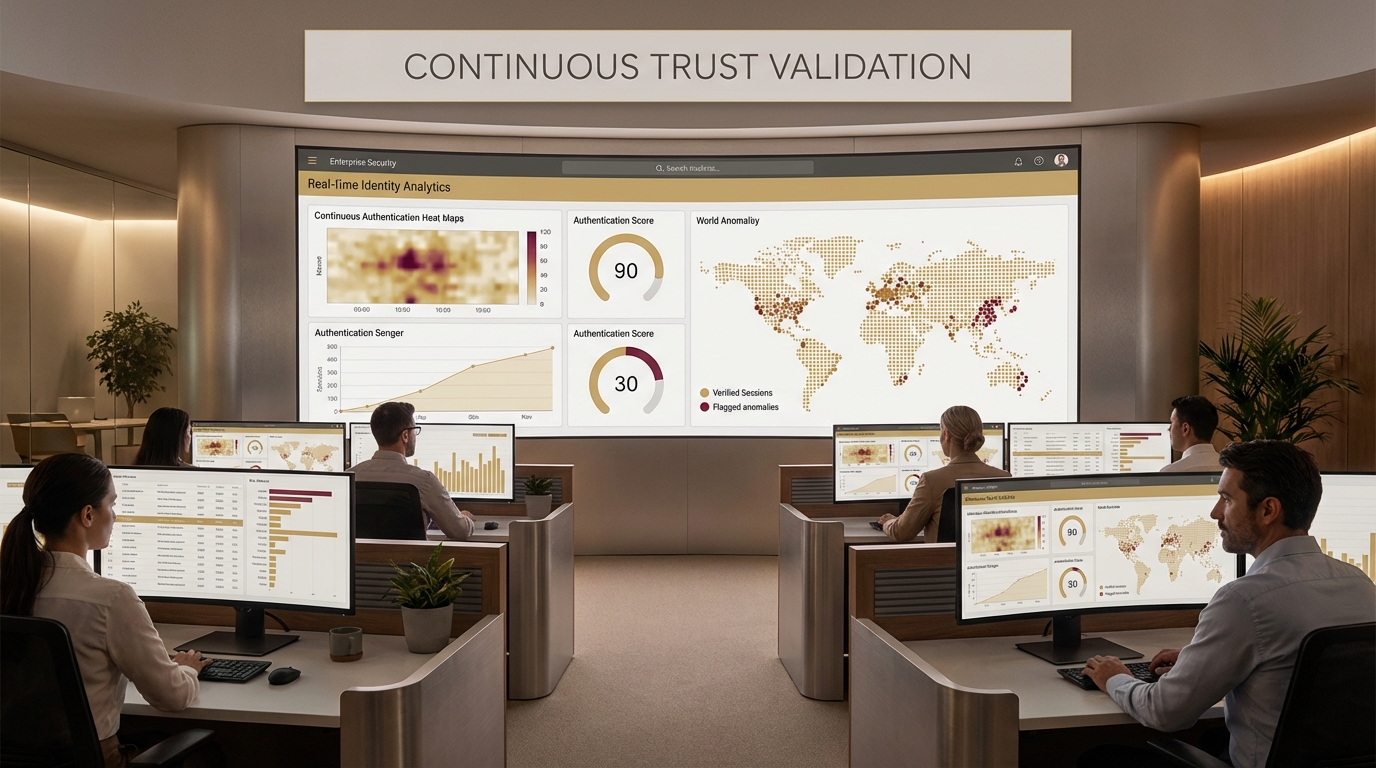
Move beyond password-based verification to continuous behavioral monitoring
Traditional authentication verifies your identity once at login and then trusts you for the duration of the session. This is like checking someone's ID at the front door of a building and then letting them roam freely for the rest of the day, even if they start behaving strangely. Continuous behavioral monitoring verifies identity constantly by analyzing patterns: typing speed, mouse movement, login times, geographic location, device characteristics, and access patterns.
If an attacker logs in with stolen credentials from a new device in an unusual location and starts accessing files the legitimate user never touches, continuous monitoring flags the session immediately. The goal is to make a stolen password insufficient on its own. Even with valid credentials, an attacker's behavior will differ from the legitimate user, and the system should detect that divergence in real time.
Identify your most valuable data and systems and protect them with stronger controls
Not all data is equally valuable, and not all systems carry the same risk. Map your crown jewels: customer databases, financial systems, intellectual property repositories, HR records, and administrative consoles. These high-value targets deserve additional layers of protection beyond standard SSO access.
Implement step-up authentication for sensitive systems, requiring a fresh verification (such as a hardware security key or biometric confirmation) each time a user accesses critical resources. Segment your network so that access to one system does not automatically grant access to all systems. Apply the principle of least privilege rigorously, ensuring employees can only access what they need for their specific role, and review those permissions quarterly.
Use threat intelligence to understand who is targeting your industry and how
Generic security measures are not sufficient against targeted attacks. Threat intelligence services can tell you which criminal groups are actively targeting your industry, what tactics they are using, and what types of credentials they are seeking. This allows you to focus your defensive investments where they will have the greatest impact.
For example, if threat intelligence reveals that a ransomware group is actively purchasing VPN credentials for healthcare organizations, a healthcare provider can prioritize VPN security, implement additional monitoring on VPN access, and accelerate their migration to zero-trust network access. Intelligence-driven defense is more efficient and more effective than trying to protect everything equally.
Elevate identity security from an IT issue to a board-level business risk
Identity compromise is not a technical problem that IT can solve alone. It is a business risk that can result in regulatory fines, customer loss, litigation, and reputational damage. Board members and executive leadership need to understand that their organization's identity is a critical asset, and its compromise represents a material financial risk.
Include identity security metrics in board reporting. Track the number of compromised credentials detected, mean time to detect and respond to identity-based attacks, the percentage of systems protected by continuous monitoring, and the results of red team exercises targeting identity infrastructure. When leadership understands the business impact in financial terms, they are far more likely to fund the necessary investments.
Monitor dark web marketplaces for your organization's stolen credentials
You cannot defend against credentials you do not know are stolen. Dark web monitoring services continuously scan criminal marketplaces, paste sites, and broker forums for credentials associated with your organization's email domains and systems. When stolen credentials are detected, you can force a password reset and investigate the scope of the exposure before the attacker uses them.
This approach directly addresses the "shelf life" problem described earlier. If your monitoring service detects your credentials on a marketplace within days of their listing, you can invalidate them before a buyer has a chance to use them. The goal is to shorten the window between theft and detection to hours rather than months. Combine dark web monitoring with infostealer log analysis to catch compromised credentials at the earliest possible stage of the supply chain.
Shorten the lifespan of credentials; rotate passwords and tokens frequently
The longer a credential remains valid, the larger the window of opportunity for an attacker. Implement aggressive rotation policies for passwords, API tokens, session tokens, and service account credentials. Consider moving to short-lived tokens that expire within hours rather than days or weeks.
For privileged accounts (administrators, service accounts with broad access), implement just-in-time access: credentials are generated on demand, last only for the duration of the specific task, and are automatically revoked afterward. This approach makes stolen credentials expire quickly, dramatically reducing the value of harvested credentials on criminal marketplaces. If a stolen token expires in four hours, the entire supply chain from harvest to compromise must complete within that window, which is vastly more difficult for attackers.
The Bottom Line
Identity is no longer just an IT problem; it is a business strategy problem. The criminal ecosystem has industrialized credential theft into a supply chain that rivals the efficiency of legitimate e-commerce. Each phase, from harvesting to brokering to monetization, has dedicated specialists, tools, and market dynamics. AI is accelerating every stage, making attacks faster, cheaper, and more convincing.
If you rely on passwords and single sign-on as your primary defense, you are bringing a checklist to an arms race. The organizations that will weather this storm are those that treat identity as a continuously verified, actively monitored, board-level business asset. They will implement behavioral analytics that detect credential misuse in real time. They will shorten the lifespan of credentials so stolen ones expire before they can be used. They will monitor the criminal marketplaces where their data is being traded. And they will ensure that a single compromised identity cannot cascade across their entire digital environment.
PwC's "Cyber Threats in Motion" report makes one thing unmistakably clear: the adversary has professionalized. The defenders must professionalize their response. That starts with accepting that identity compromise is not a matter of "if" but "when," and building systems that detect, contain, and recover from breaches quickly rather than relying solely on prevention.
This article is part of our incident analysis newsletter series. Subscribe to receive complete analyses with timeline tables, risk matrices, governance checklists, and actionable recommendations.


