In this issue — 4 parts
Part 1 of 4
A Trusted Source Becomes the Weapon
The Problem: A Trusted Source Becomes the Weapon
Think of it like this: imagine you buy groceries from a trusted supermarket every week. You know the store, you trust the brands on the shelves, and you never think twice about bringing those products home. What you do not know is that someone broke into the supermarket's warehouse and laced some of the products with a substance that quietly reports back everything in your fridge. The packaging looks perfectly normal. The store's name is still on the receipt. You have no reason to check. Within three days, millions of shoppers have brought contaminated products into their homes without a single alarm going off.
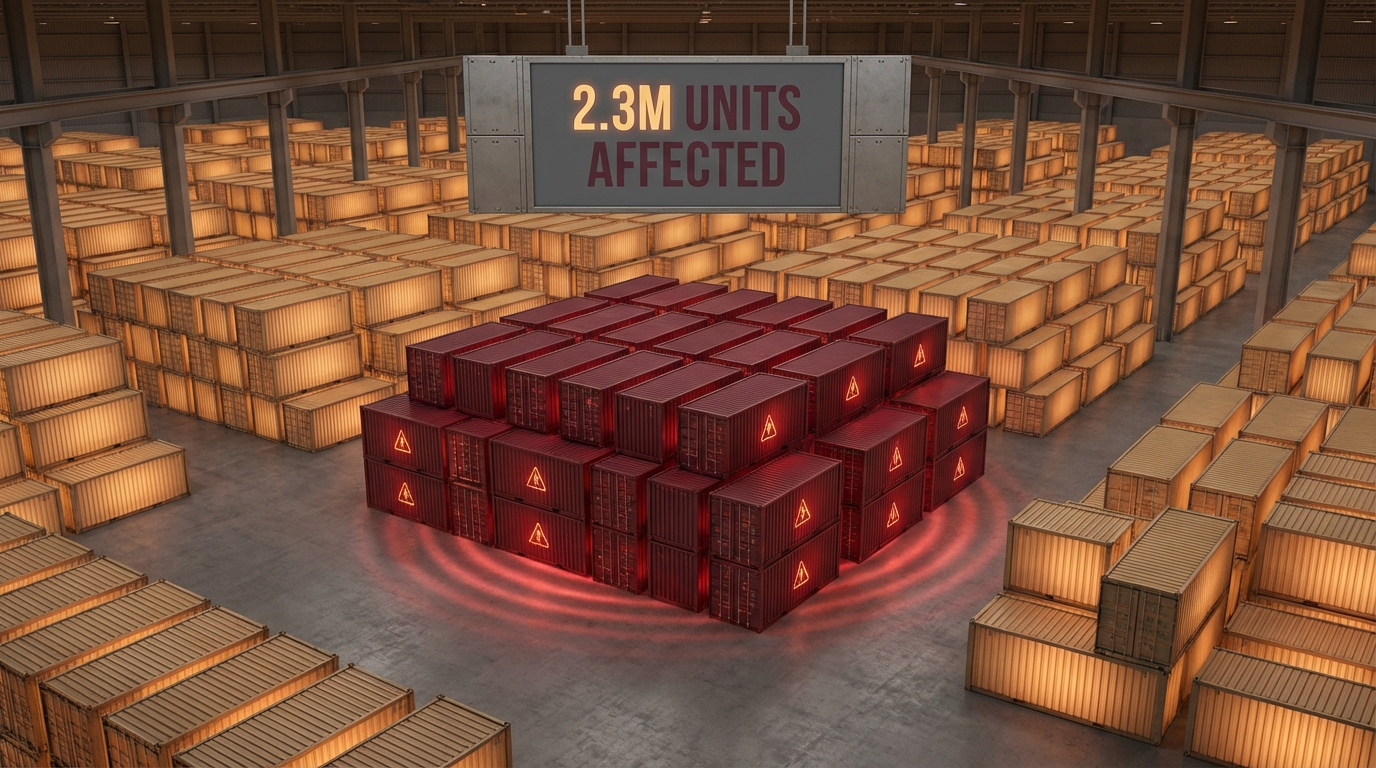
That is exactly what happened to 2.3 million software developers in March 2026 when attackers poisoned the software supply chain of popular AI development tools.
To understand why this attack was so devastating, you need to understand what a "software supply chain" is. Modern software is not written from scratch. Developers assemble their applications from thousands of pre-built components, each maintained by different teams around the world. These components are distributed through centralized registries (similar to app stores but for code) and developers download them automatically as part of their build process. This chain of trusted software components that developers rely on to build their own products is the software supply chain.
The reason supply chain attacks are so effective is simple: you poison one ingredient and every product that uses it becomes contaminated. Instead of breaking into thousands of companies one at a time, an attacker compromises a single popular component and lets the distribution system do the rest. The trust that makes the ecosystem efficient is the same trust that makes it vulnerable.
This particular attack targeted LiteLLM, a widely adopted tool that acts as a universal translator between applications and AI services like OpenAI, Anthropic, and Google. Because LiteLLM sits at the intersection of AI development and cloud infrastructure, compromising it gave attackers access to the most sensitive credentials in any developer's environment: API keys for AI services, cloud access tokens for AWS, Google Cloud, and Azure, and authentication secrets for internal systems. It was the equivalent of poisoning the one ingredient that goes into every dish at every restaurant in the city.

Attackers compromised the build infrastructure of popular AI tools, turning trusted software distribution channels into malware delivery pipelines that reached 2.3 million developer environments in 72 hours.
Why This Matters to You
If your organization builds software, uses AI services, or relies on cloud infrastructure, you are part of a software supply chain. Every developer tool, every library, and every build pipeline is a potential entry point. This attack demonstrated that even well-maintained, popular open-source projects can be silently weaponized, and the damage spreads at machine speed.
The attackers did not need to find a vulnerability in the software itself. They compromised the process that builds the software. That distinction is critical: code review, security audits, and vulnerability scanning all examine the source code, but this attack injected malicious behavior at the build stage, after all those checks had already passed.
Coming up in Part 2 — the full anatomy of how a trusted source became the weapon.
Part 2 of 4
Anatomy of a Supply Chain Attack
What you missed: a trusted software source was turned into the weapon — the update you were supposed to trust carried the attack.
What Happened: Anatomy of a Supply Chain Attack
The attack unfolded in a precise sequence over the course of several weeks. Each step built on the last, and by the time anyone noticed, millions of environments were already compromised. Here is the full chain of events, explained step by step.
The attack cascaded from a single compromised build system to millions of developer environments, harvesting credentials at every stage and using them to penetrate deeper into organizational infrastructure.
Build Infrastructure Compromised
Attackers gained access to the CI/CD (Continuous Integration/Continuous Delivery) build infrastructure used by LiteLLM, a popular AI tool that routes requests to services like OpenAI, Anthropic, and Google. CI/CD systems are the automated assembly lines that turn source code into finished software packages. By compromising this system, attackers controlled the factory floor itself.
The initial breach likely occurred through stolen credentials or a vulnerability in the CI/CD platform. Once inside, the attackers had the ability to modify the build process without touching the source code.
Build Process Poisoned
The attackers injected malicious code into the build process itself, not into the source code repository. This is a crucial distinction. Anyone reviewing the project's source code on GitHub would see clean, legitimate code. The malicious payload was added during the build stage, after the code had been reviewed and approved. Every new version of the package would automatically carry the payload without any visible change to the codebase.
This technique bypasses code review, pull request approvals, and static analysis tools because none of those processes examine the build pipeline output.
Legitimate Distribution
Poisoned packages were signed with the project's legitimate cryptographic keys and distributed through the normal package registry channels. The packages had correct version numbers, valid signatures, and appeared in the expected locations. There was no indication that anything had been tampered with. Automated security tools that check package signatures would have verified these packages as authentic.
The signing keys were part of the build infrastructure the attackers controlled. This meant the malware carried a stamp of authenticity that security tools were designed to trust.
Rapid Automated Spread
Within 72 hours, 2.3 million developer environments automatically downloaded the compromised packages. Most modern development workflows use automated dependency management that pulls the latest versions of tools without manual intervention. Developers set their systems to automatically grab the latest version because staying current with security patches is considered best practice. In this case, that best practice became the attack vector.
Auto-update is dangerous in this context: the very mechanism designed to keep developers safe (automatic patching) became the delivery system for malware.
Credential Harvesting
Once installed, the malicious code silently harvested AI API keys (for OpenAI, Anthropic, Google, and other providers), cloud credentials (AWS access keys, GCP service account tokens, Azure credentials), and other secrets stored in environment variables and configuration files. The exfiltration was designed to mimic normal network traffic, making it extremely difficult to detect with standard monitoring tools.
Because LiteLLM is specifically designed to work with AI API keys, it had a legitimate reason to access these credentials, making the theft invisible to behavioral monitoring.
Infrastructure Penetration
Stolen API keys were immediately used to run up six-figure AI usage bills on victims' accounts. More critically, the harvested cloud credentials gave attackers access to entire infrastructure stacks. A single compromised developer laptop with AWS credentials could provide access to production databases, internal services, customer data, and deployment pipelines. The credential cascade turned a developer tool compromise into full organizational breaches.
The "credential cascade" effect meant that one stolen key often led to access to systems that contained more keys, expanding the blast radius exponentially.
Massive Remediation Costs
Remediation costs were estimated at $500K to $5M per affected organization. These costs included forensic investigation to determine the scope of compromise, credential rotation across all potentially affected systems, infrastructure rebuilds for any system that may have been accessed with stolen credentials, legal and compliance obligations including breach notification, customer communication and potential regulatory fines, and extended monitoring to ensure attackers had not established persistent access through other means. Many organizations discovered that they could not determine with certainty which systems had been accessed, forcing them to assume worst-case scenarios and rebuild from scratch.
The true cost of this incident extends far beyond the initial financial impact. Organizations that lost customer trust, faced regulatory action, or suffered intellectual property theft may never fully recover.
The Broken Trust Chain
"The package comes from a trusted, well-known open-source project."
"The code has been reviewed by the community and the maintainers."
"The package is signed and verified; it is safe to install automatically."
"Auto-updating keeps us safe by ensuring we always have the latest patches."
A reasonable set of assumptions that held true for years.
The build system was compromised; the trusted project unknowingly distributed malware.
The malicious code was injected after code review, during the build stage that nobody monitors.
Every new version carried the payload, signed with legitimate keys; verification tools approved it.
Auto-update delivered the compromised version to 2.3 million environments in 72 hours.
Every assumption was violated. The trust model failed at every level.
The software supply chain operates on implicit trust. When that trust is violated at the build infrastructure level, every downstream consumer is exposed because there is no independent verification between what was built and what was expected.
Coming up in Part 3 — the true cost of a supply-chain breach, from API charges to an insurance gap.
Part 3 of 4
The True Cost of a Supply Chain Breach
What you missed: the full anatomy: compromised build infrastructure, poisoned builds, legitimate distribution, automated spread, credential harvesting, and the broken trust chain behind it.
Financial Impact: The True Cost of a Supply Chain Breach
The financial damage from this attack unfolded across multiple dimensions, each compounding the last. What began as stolen API keys quickly escalated into an organizational crisis for thousands of companies worldwide.
Financial Impact
Six-figure unauthorized API usage charges, credential cascade granting access to entire infrastructure stacks, and incident response costs between $500K-$5M per organization.
Unauthorized API Charges
Stolen API keys were used to make massive numbers of requests to AI services. Some organizations discovered six-figure charges on their OpenAI, Anthropic, and Google AI accounts within days. Because these requests were made using legitimate credentials, the AI providers processed them as normal usage. Disputing these charges proved extremely difficult; most AI service agreements hold the account holder responsible for all usage associated with their keys, regardless of whether the usage was authorized. Several affected companies reported that their cloud providers initially declined to reverse the charges, citing terms of service.
Credential Cascade
The stolen cloud credentials (AWS, GCP, Azure) created a cascading access problem. A single developer's compromised AWS access key could grant access to S3 buckets containing customer data, RDS databases with financial records, Lambda functions with hardcoded secrets to other services, and IAM roles that provide access to additional accounts. Organizations that followed the common but insecure practice of storing credentials in environment variables found that one breach point led to total infrastructure compromise. The cascade effect meant that the blast radius of the attack grew exponentially once credentials started flowing to the attackers.
Remediation Per Org
Incident response costs included forensic investigation (determining what was accessed), complete credential rotation (every key, token, and certificate that could have been exposed), infrastructure rebuilds (any system accessed with stolen credentials had to be treated as compromised), legal counsel for breach notification compliance, customer communication and potential regulatory fines under GDPR, CCPA, and other frameworks, and extended monitoring contracts to watch for residual attacker access. Many organizations also faced insurance disputes, as cyber insurance policies often contain exclusions for supply chain attacks or require specific security controls that the policyholder may not have had in place.
The Insurance Problem
Several affected organizations reported disputes with their cyber insurance carriers. Supply chain attacks occupy a gray area in many policies. Insurers argued that the compromise originated from a third-party component, not from a direct attack on the insured organization, and that coverage exclusions for "failure to maintain adequate security controls" applied because the organization had not implemented dependency pinning or build verification.
This incident is expected to reshape the cyber insurance market. Underwriters are now beginning to require evidence of software supply chain security controls (dependency pinning, SBOM maintenance, build provenance verification) as prerequisites for coverage. Organizations that cannot demonstrate these controls may face higher premiums or coverage exclusions in future policy renewals.
Coming up in Part 4 — six steps to protect your organization from the next poisoned update.
Part 4 of 4
Six Steps to Protect Your Organization
What you missed: the true cost: unauthorized API charges, a credential cascade, per-org remediation, and an insurance gap.
What You Can Do: Six Steps to Protect Your Organization
The good news is that every stage of this attack could have been mitigated or detected with the right controls in place. None of these defenses require exotic technology. They require discipline, planning, and a willingness to trade some convenience for security. Here are six practical steps that any organization can implement, explained in terms that do not require a security background.

Effective defense against supply chain attacks requires layered controls: pinning versions, verifying integrity, isolating build environments, and maintaining the ability to respond quickly when compromise is detected.
Pin exact versions and review before updating
Instead of allowing your systems to automatically grab the latest version of every dependency, lock each component to a specific, tested version. Think of it like inspecting each delivery before putting it on the shelf instead of accepting every shipment sight unseen. When a new version becomes available, treat the update as a deliberate decision that includes reviewing changelogs, checking for anomalies, and testing in an isolated environment before deploying to production.
This single control would have prevented the automatic spread of the poisoned packages. If developers had been running pinned versions, the compromised builds would have sat in the registry without being downloaded until someone deliberately chose to update, at which point the compromise might have been detected.
Maintain a complete Software Bill of Materials (SBOM)
An SBOM is a complete inventory of every component in your software, similar to an ingredient list on food packaging. When a supply chain compromise is announced, organizations with an SBOM can immediately determine whether they are affected and which systems need attention. Without one, the investigation starts with "we do not know what we are running," which adds days or weeks to incident response.
Maintaining an SBOM also provides visibility into your transitive dependencies: the components that your components depend on. In many supply chain attacks, the compromised package is not one you chose directly; it is a dependency of a dependency, buried several layers deep. An SBOM surfaces these hidden relationships so you can assess your exposure before an incident occurs.
Build in sandboxed environments isolated from production credentials
Your build process should never have access to production secrets. If a compromised dependency runs during the build, it should find nothing valuable to steal. Sandboxed build environments are like constructing a building inside a sealed room: even if something goes wrong during construction, it cannot affect anything outside that room.
In this attack, many of the harvested credentials were accessible because developers built and tested software on the same machines (or in the same cloud environments) that had access to production infrastructure. Strict separation between build environments and production environments would have limited the attacker's access to test credentials with no real value, rather than production keys that unlocked entire infrastructure stacks.
Store credentials in secure vaults, not environment variables
Environment variables are the most common way developers store API keys and cloud credentials, and they are also the easiest for malicious code to read. Any process running on the machine can access them. A secure vault (such as HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault) provides credentials on demand with access logging, automatic rotation, and the ability to revoke access instantly.
Think of it this way: storing credentials in environment variables is like keeping all your keys on a hook by the front door where anyone who enters the house can grab them. A vault is like keeping them in a safe that requires identification, logs every access, and can be locked remotely if the house is compromised. The extra friction is a feature, not a burden; it means that malicious code running in your environment cannot silently harvest credentials without triggering an audit trail.
Verify the integrity of every package before deploying
Beyond checking signatures (which can be forged when build infrastructure is compromised), implement reproducible builds and independent verification. A reproducible build means that anyone can take the same source code and build process and produce an identical output. If the package you downloaded does not match what you would get by building the source code yourself, something has been tampered with.
Organizations should also maintain checksums of known-good versions and compare new downloads against expected values. Consider using a private package mirror that you control, where packages are scanned and verified before being made available to your developers. This adds a buffer between the public registry and your internal systems, giving you time to detect compromised packages before they reach developer machines.
Have a plan for rapid credential rotation when compromise is detected
When a supply chain compromise is announced, the clock is already running. Every minute that passes with exposed credentials is a minute the attacker can use them. Organizations need a pre-built, tested runbook for rotating all credentials across their infrastructure, and they need to be able to execute it in hours, not days. This includes API keys for AI services, cloud provider access keys, database passwords, SSH keys, TLS certificates, and any other secrets that may have been accessible to the compromised component.
The organizations that fared best in this incident were those that had automated credential rotation procedures already in place. They were able to revoke and replace all potentially exposed credentials within hours of the advisory being published, limiting the attacker's window of opportunity. Organizations that relied on manual processes took days or weeks to complete rotation, during which time their credentials remained active and exploitable.
The Bottom Line
The software industry runs on trust, and this incident proved that the trust model is broken. Developers trust that the packages they download are the same packages the maintainers intended to publish. They trust that build systems are secure. They trust that signed packages are safe. And they trust that auto-updating keeps them protected. Every one of those assumptions failed in this attack.
Auto-updating from unverified sources is like leaving your front door open and trusting that only friends will walk in. It works until it does not, and when it fails, the consequences are catastrophic. The convenience of automatic dependency management has masked a fundamental security gap: there is no independent verification between what a developer intends to publish and what millions of consumers actually receive.
This is not a problem that individual developers can solve alone. It requires a shift in how the entire industry thinks about software distribution. Build provenance, reproducible builds, dependency pinning, and SBOM maintenance need to become standard practice, not optional extras for security-conscious teams. Until that shift happens, every organization that depends on open-source software (which is nearly every organization on Earth) remains one compromised build pipeline away from a catastrophic breach.
This article is part of our incident analysis newsletter series. Subscribe to receive complete analyses with timeline tables, risk matrices, governance checklists, and actionable recommendations.



